Highly scalable
Fully managed
Reliable and secure
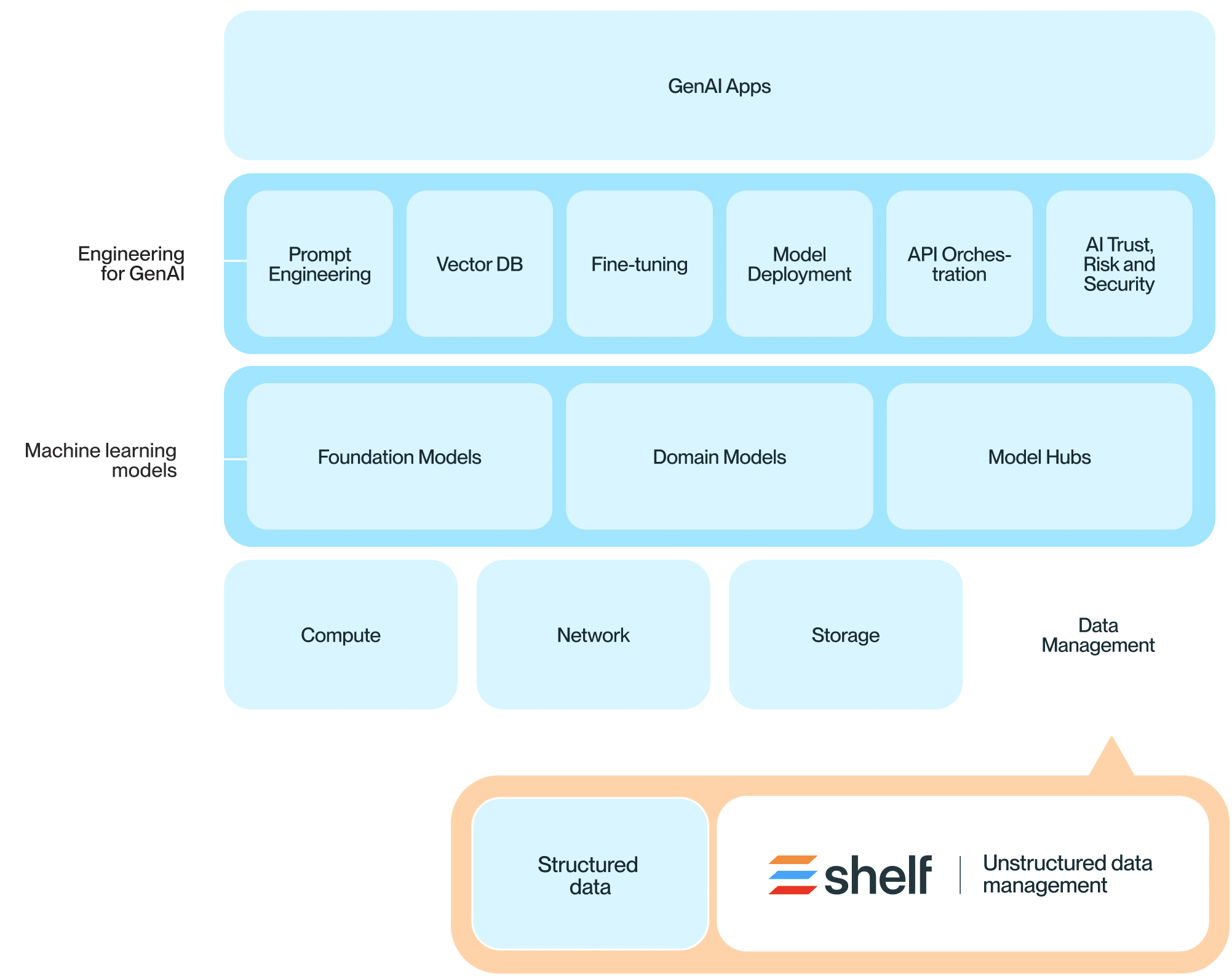
Your future-proof knowledge platform
Designed to meet the demands of tomorrow, our platform offers unmatched scalability, management, and security.
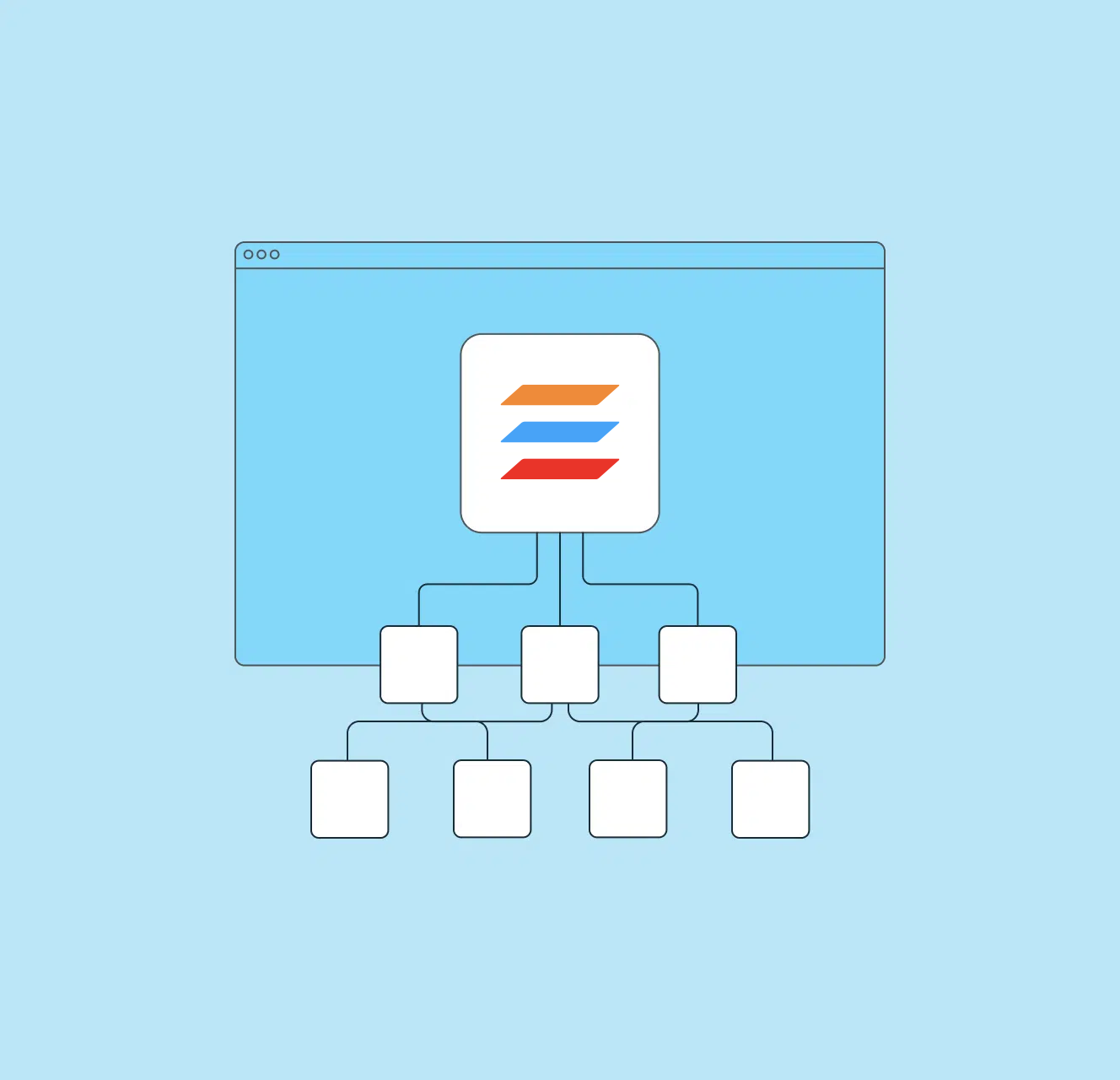
Future-ready, scalable and integrative architecture
- Modern and highly scalable platform
- Microservices with API-first architecture
- Limitless real-time processing and retrieval
- Python and Node SDKs
- Built for easy integration
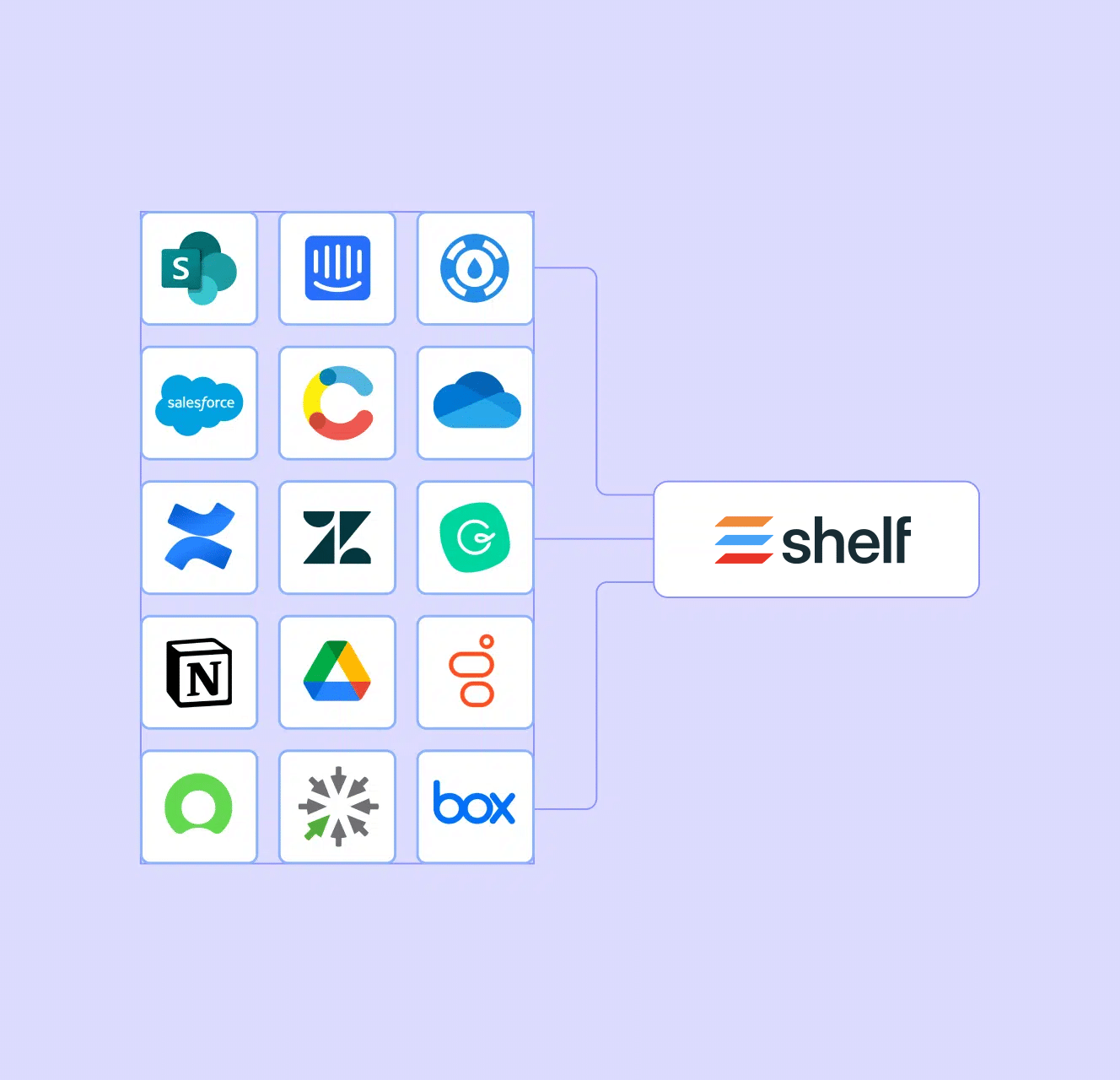
Seamless content integration
- Pre-built content connectors
- Custom connector framework
- Unlimited real-time processing and retrieval
- Different file types normalized into JSON
- Access permissions with user groups
Proven security and compliance
- Enterprise-grade security and encryption
- Data Residency Requirements met for US/EU/CA
- Regular external security assessments
- Regular cross-region backups
- SOC 2 Type II certified
Security, availability and confidentiality trust

EU-compliant data protection protocols

Application security & governance framework
Secure user access and compliance
- SSO & SCIM support
- Granular user group based permissions
- Granular API scopes and permissions
- Easy to understand access rules
- Extensive user management
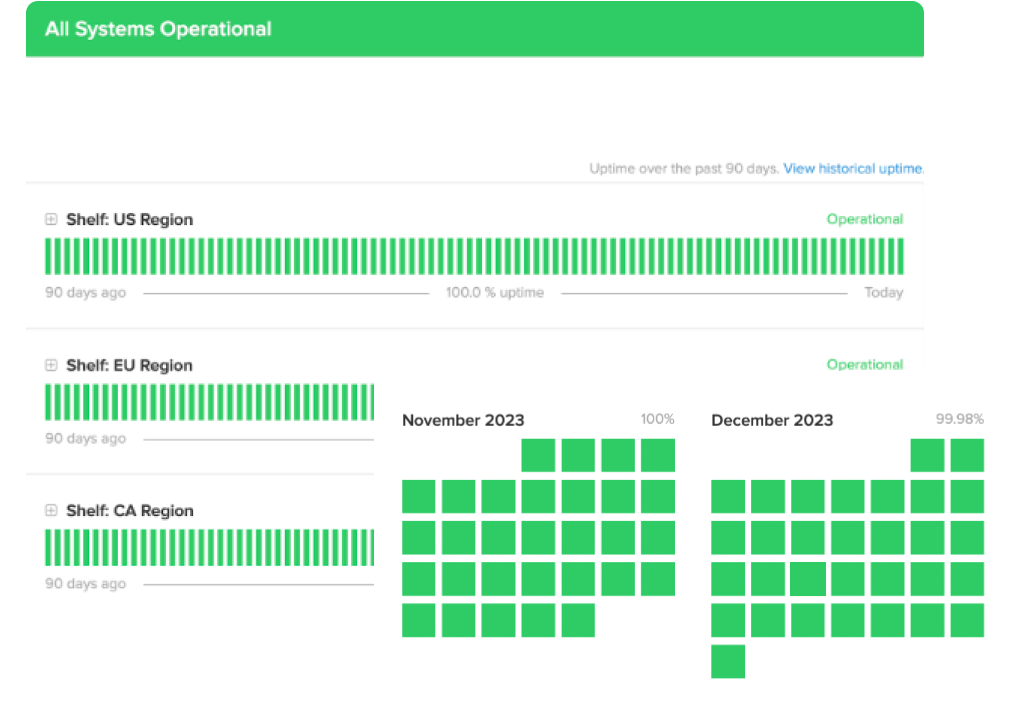
Built for uptime and resilience
- Historic uptime at 99.99%
- Built on AWS with data center redundancy
- Multi-availability zones within each data center
- Data centers in the US, Canada and EU
- Real-time System Status
Efficient data management
- Terabytes of data processed daily
- 50+ file types supported
- Real-time & batch processing
- Versioning and change history
- Encryption in transit and at rest
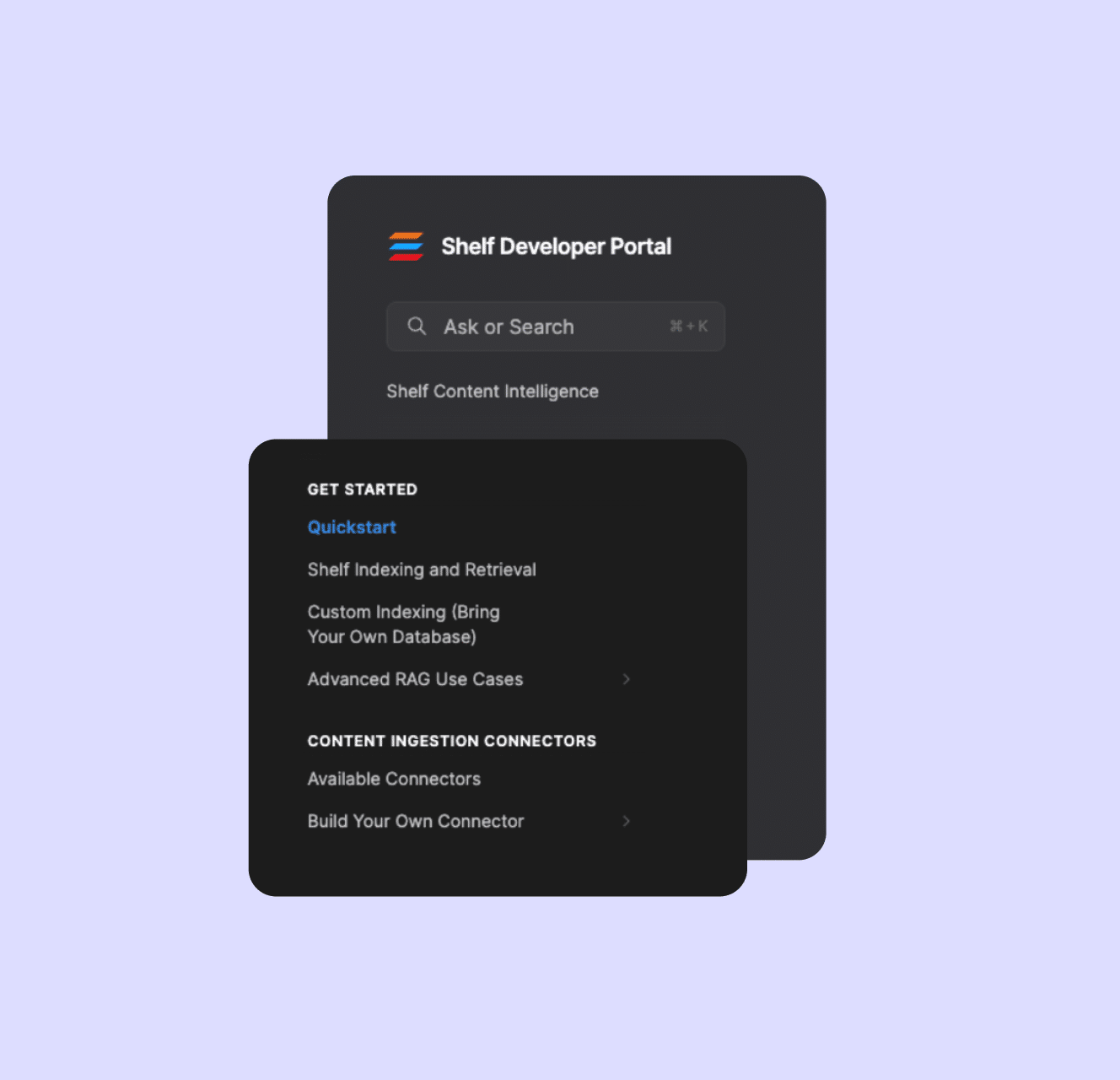
Comprehensive & developer-centric documentation
- Dev Portal with full API Specs
- Cookbooks with reference implementations
- Use case and best practice guides
- Python and Javascript SDKs
- Open Source contributions
Request documentation via Whistic
Shelf uses Whistic to securely share company and product security profiles as well as detailed documentation required for vendor security assessments.
Request DocumentationSecurity FAQ
What kind of infrastructure supports your services?
Our services are hosted on leading cloud infrastructure with advanced network and perimeter protection.
How do you defend against web-based attacks?
We deploy a web application firewall and DDoS protections to safeguard against external threats.
What measures are in place for detecting vulnerabilities?
We conduct regular vulnerability scanning and annual penetration testing to identify and mitigate risks.
What certifications validate your security measures?
We are SOC2 Type II certified, reflecting our commitment to high security standards.
How do you ensure business continuity in case of an incident?
Our business continuity planning prepares us to maintain operations and security under various scenarios.
How do you manage organizational security?
We maintain a strong focus on security awareness, training, and 24/7 risk management to ensure our staff is prepared to identify and mitigate risks.
What is your approach to managing risks from vendors?
Vendor risk management processes are in place to ensure all third-party services meet our stringent security standards.
Data privacy FAQ
What measures are in place to protect customer data?
We use logical tenant separation, encryption in transit (TLS 1.2+), and encryption at-rest (AES-256) to ensure data protection.
How do you comply with GDPR and CCPA regulations?
We are compliant with GDPR and CCPA, ensuring all data handling respects privacy laws and user rights.
Can users opt out of AI-driven features?
Yes, users have the option to opt out of AI features to maintain control over their data usage.
What standards do you follow for data security compliance?
We adhere to SOC2 Type II and perform various self-assessments including CAIQ, VSA, and PCI.
How is AI data managed to ensure privacy?
AI models are hosted securely, with no data sharing across tenants for LLM training and fine-tuning.
What ongoing practices ensure continued data privacy compliance?
Regular audits, continuous monitoring, and updates to our practices ensure we remain compliant with evolving privacy laws.
What frameworks guide your AI security practices?
We follow the OWASP Top 10 LLM Framework and GenAI Security & Governance Framework to ensure the security and governance of our AI implementations.
See Shelf Platform in action